How to Configure RDP when Remotely Connecting to an Entra‑Enrolled Device (Windows 10/11)
📌 Overview
These steps describe how to configure Remote Desktop (RDP) to successfully connect to a Microsoft Entra ID (Azure AD) joined device over VPN or office network. This includes editing the .rdp connection file and optionally editing the Windows hosts file on the VPN client to resolve NetBIOS or FQDN names more reliably.
Heavily based on these three articles and built from ticket #2571
Especially useful for Santiam Water Control District staff.
https://learn.microsoft.com/en-us/windows/client-management/client-tools/connect-to-remote-aadj-pc
https://rublon.com/blog/how-to-rdp-into-azure-ad-joined-vm
https://www.howtogeek.com/27350/beginner-geek-how-to-edit-your-hosts-file
✅ Requirements & Prerequisites
- Remote device: Windows 10 version 1809 or later, or Windows 11 (with Oct‑2022 cumulative update or newer) joined to Microsoft Entra ID. (Microsoft Learn, Microsoft Learn)
- Local client device: Running Windows 10 or 11. It can be Entra joined, hybrid joined, registered, or even part of a different AD domain. (Microsoft Learn)
- Ensure the remote device (host) is configured to allow RDP: under Settings → System → Remote Desktop, “Allow Remote Desktop connections” is enabled. (Microsoft Learn)
- If enabling Azure AD authentication, the remote device doesn’t need Network Level Authentication enforced; indeed disabling NLA may be required for this use case. (Microsoft Learn)
🛠 Step 1 – Edit the .rdp file
- On your local client, launch Remote Desktop Connection (
mstsc.exe), enter the hostname (NOT the IP Address, often fails in this setup) of the remote device, expand Show Options, and click Save As… to store a.rdpfile locally. (Stack Overflow) - Open the saved
.rdpfile using a text editor like Notepad. - Update the
full address:s:field to use the NetBIOS hostname or FQDN, not the IP address. Example:full address:s:Desktop‑Manager(Replaces earliers: \\192.168.1.119usage.) (ronamosa.io)
Your internal ticket notes confirm that Azure AD–joined devices cannot be reached by IP if using Azure AD authentication—they require name resolution.enablecredsspsupport:i:0 authentication level:i:2This disables CredSSP and sets a proper authentication level for Azure AD RDP login. (Stack Overflow) - Additionally, to enable Microsoft Entra (Azure AD) authentication prompt via RDP, add (or change) the following:
enablerdsaadauth:i:1This flag ensures the client uses the web-account sign‑in flow. Without it, authentication via Azure AD may fail. (Microsoft Learn) - Save the file and double-click it to initiate RDP.
- At credential prompt, enter your username in full UPN format:
username@domain.comYou will be prompted to fully sign in through a popup Microsoft login window and approve this new host; accept it. (Rublon, Microsoft Learn)
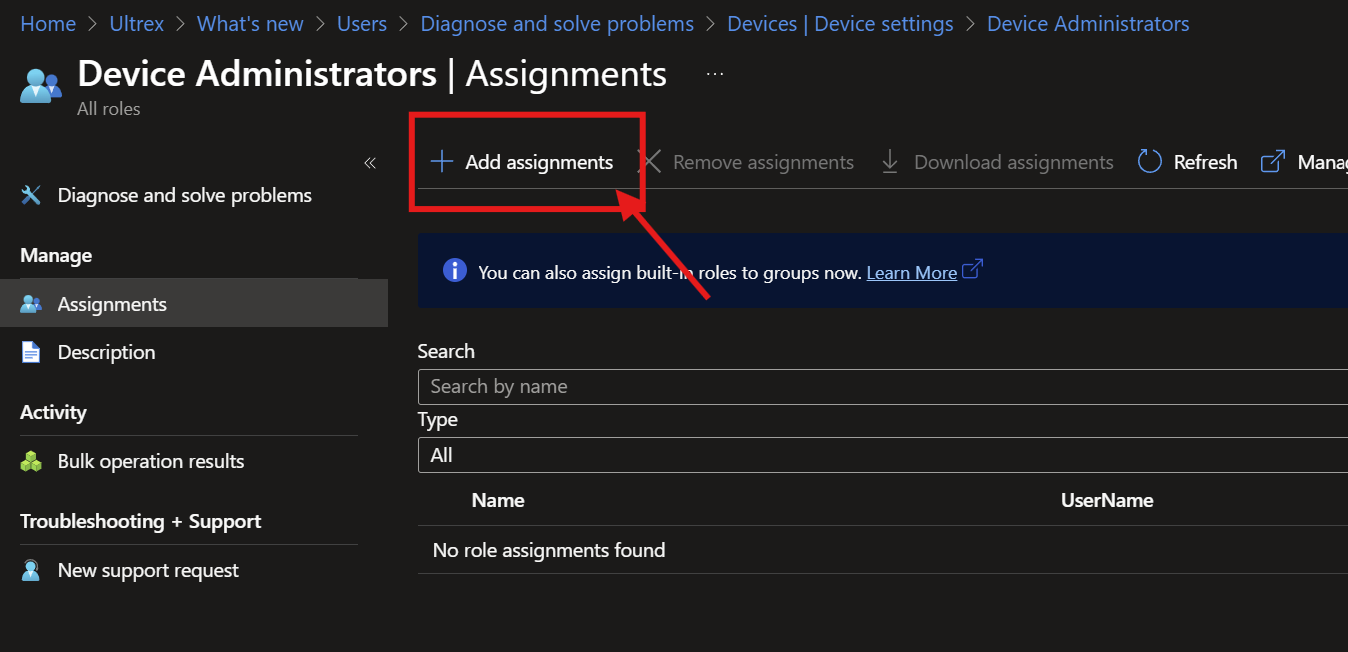
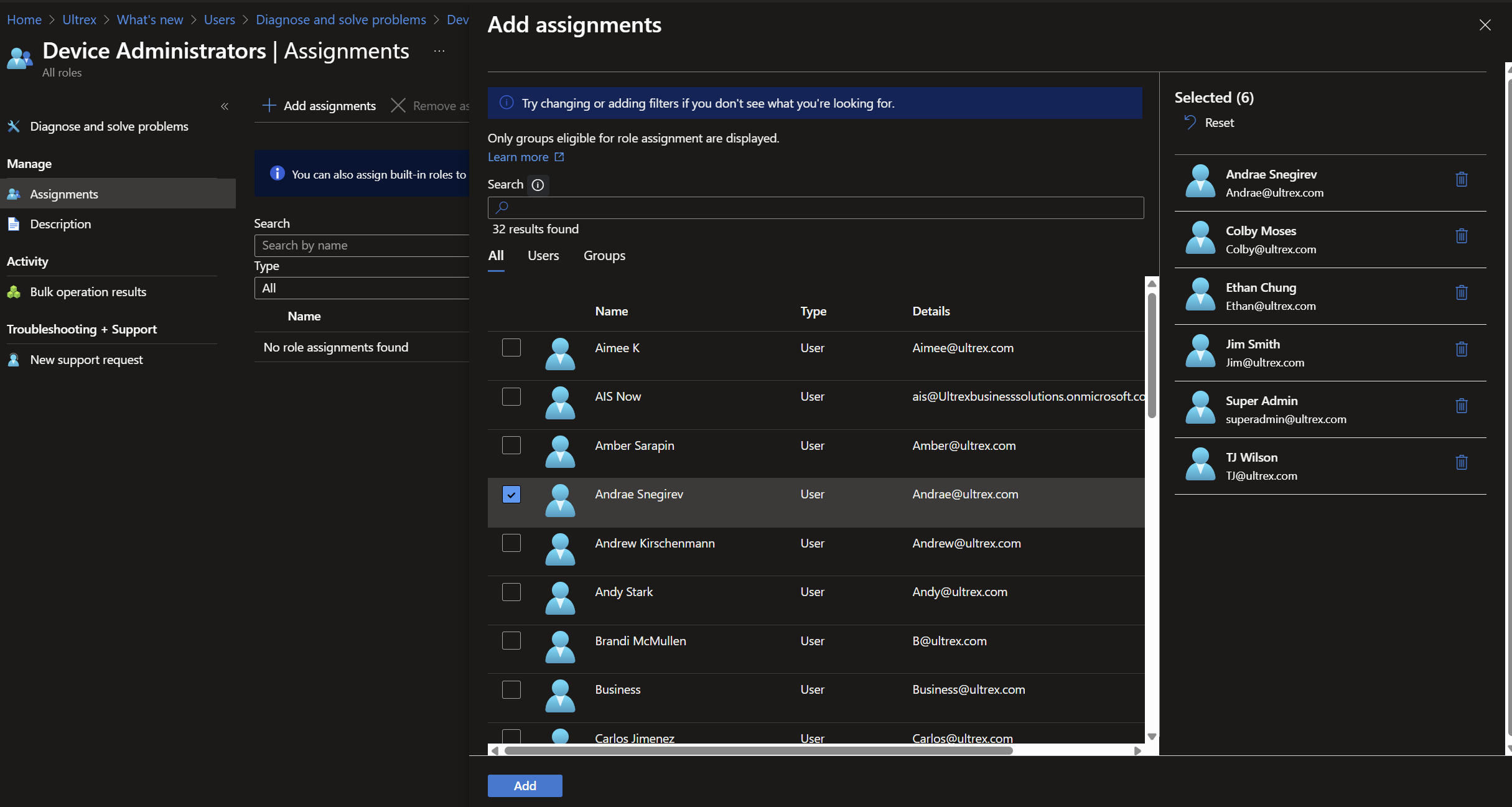
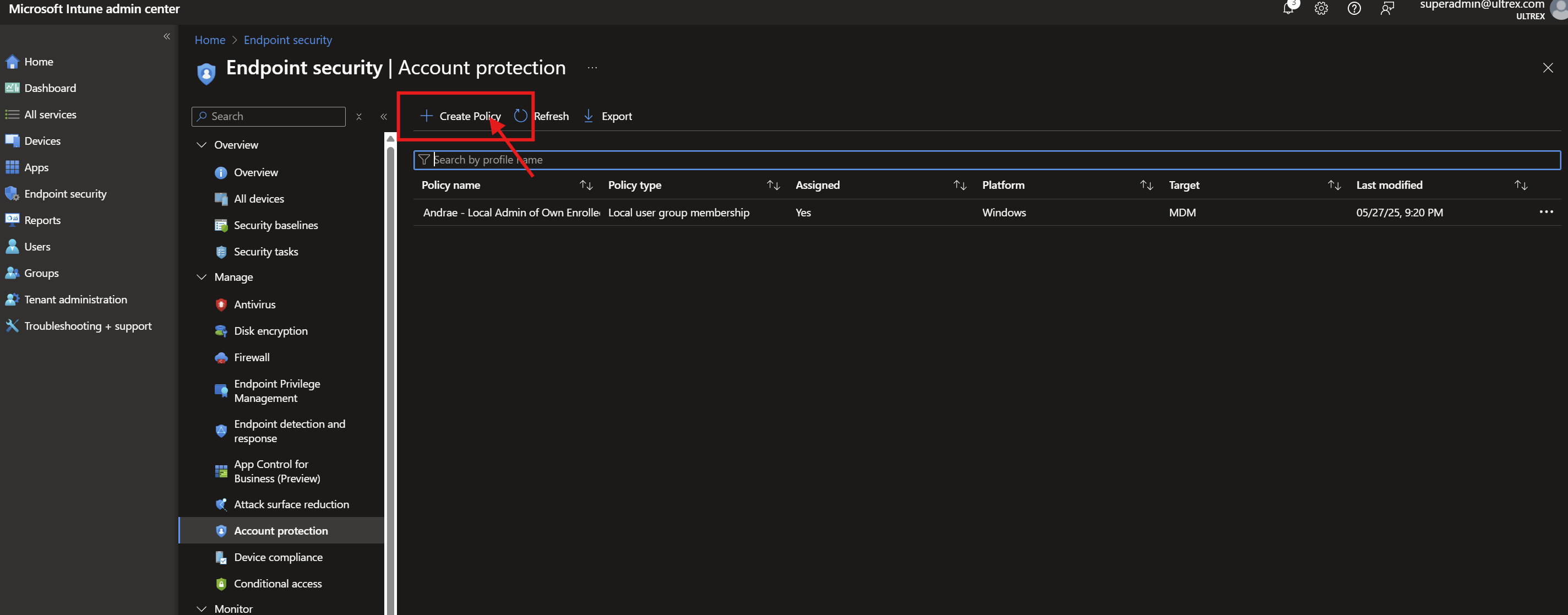
🧪 Step 2 – (Optional) Add the Azure AD user to the Remote Desktop Users group
If you are not already part of the Remote Desktop Users group on the remote device, you may need to add your account or Azure AD group to it via local admin or MDM policy:
- Using Command Prompt (as administrator):
net localgroup "Remote Desktop Users" /add "AzureAD\username@domain.onmicrosoft.com" - Or using PowerShell:
Add-LocalGroupMember -Group "Remote Desktop Users" -Member "AzureAD\username@domain.com"(Prajwal Desai)
🧭 Step 3 – (Optional) Edit the hosts file for name resolution over VPN
When your client cannot resolve NetBIOS names over a VPN Connection or Wi‑Fi, you can manually define them:
- On the remote client machine, open the hosts file in an elevated editor. Search for Notepad and Run as Administrator > File > Open to the following path:
C:\Windows\System32\drivers\etc\hosts - Add entries mapping internal device names to their IP addresses:
192.168.1.119 Desktop‑Manager - Save the file. This allows the host name used in your
.rdpfile to resolve correctly even if DNS or NetBIOS resolution fails.
🧩 Troubleshooting Scenarios & Notes
- VPN client cannot ping or resolve NetBIOS name: may stem from missing NetBIOS over TCP/IP setting, wireless isolation, subnet differences, or routing rules. Ensure NetBIOS over TCP/IP is enabled in adapter IPv4 → Advanced → WINS tab, and review network isolation settings.
- RDP fails using IP address: Azure AD joined devices require name (hostname or FQDN). IP‑only connections do not support the Azure AD authentication flow; using a host‑mapped name is required. (Microsoft Learn, Microsoft Learn)
- NLA required: if NLA is enforced, Azure AD authentication may fail; ensure the remote device has NLA disabled if running into connection issues. (Microsoft Learn, niallbrady.com, Microsoft Learn)
✅ Example .rdp snippet
Note: some of these are already added in, so only copy and paste the missing ones and change the relevant entries.
full address:s:Desktop‑Manager
enablecredsspsupport:i:0
authentication level:i:2
enablerdsaadauth:i:1
ℹ️ Why these settings matter
- enablerdsaadauth:i:1 toggles the web‑account Azure AD login experience, prompting or allowing authentication through Entra ID. Without it, RDP will not negotiate Azure AD credentials correctly. (Microsoft Learn)
- enablecredsspsupport:i:0 avoids CredSSP pitfalls that block Azure AD authentication, especially when Network Level Authentication isn’t compatible with Entra‑based tokens. (Stack Overflow)
- authentication level:i:2 is the required setting for secure fallback when CredSSP is disabled. (Stack Overflow)
📌 Final Notes
- Always ensure both client and remote satisfy Windows update and version prerequisites for Azure AD RDP support. (Microsoft Learn)
- Use FQDN or hostname resolution rather than IP when targeting Entra‑joined devices, especially in VPN environments.
- The hosts file edit can be a reliable workaround when DNS or NetBIOS resolution fails.